Of all of the frequent PC safety threats right this moment, ransomware could be the most pernicious and painful for customers. Not solely can it lock up your system and forestall you from accessing your PC and information, however it could additionally ship all of your information to attackers over the web and probably give them entry to your on-line accounts via the saved credentials in your browser.
For victims of ransomware, the sudden sense of panic because the display screen shows a message that the PC has been contaminated—they usually should pay to regain management—usually turns to rage as they try and get to their information again after which understand the terrible fact. If you’ve been hit ransomware, preserve your cool and don’t ship any cash to the attackers.
In this information, we’ll provide you with essential tricks to stop a ransomware assault, and the inform you what to do in case your PC is ever contaminated.
Further studying: PCWorld’s top picks for security software suites
How to stop a ransomware assault
As I defined in my lexicon of security terms, ransomware is a kind of malware that locks you out of your system with the intention of extorting cash from you to liberate your machine and information. The finest time to cope with a ransomware assault is earlier than one even occurs. Here are 4 issues you are able to do to keep away from being a sufferer within the first place, or be higher ready to shortly recuperate in case you do find yourself falling prey.
1. Keep your information within the cloud
By maintaining all of your essential information on-line as a substitute of totally counting on native storage, you’ll be much less weak to shedding something you care about in case your laborious drive is ever maliciously encrypted (or just fails). In my case, I’ve been utilizing a redundant hybrid cloud setup for years as a result of I change computer systems continuously. Because all my pictures and information are saved and backed up in a number of locations—each in my dwelling and within the cloud—I’ve no hassle organising a brand new PC and wiping an previous one any time I really feel prefer it.
2. Use a firewall
Modern Wi-Fi routers with strong firewalls might help take the sting out of phishing assaults and clicking dangerous hyperlinks. This is particularly essential when you have children or different customers within the family who is likely to be susceptible to clicking malicious hyperlinks. Consider selecting a router with robust firewall options, such because the Orbi 970, which features a BitDefender-backed safety service that routinely detects identified malicious websites and gained’t allow you to load them in your browser.
Better but, set up a devoted firewall equipment just like the Firewalla Gold SE, which has glorious computerized risk detection, intrusion detection, advert blocking, and a number of different killer security measures.
Jim Martin / Foundry
3. Keep your antivirus turned on and up-to-date
A fundamental antivirus is healthier than none in any respect, as long as you retain it up to date. Whether you rely solely on the built-in Windows Security (right here’s a full how-to on activating ransomware protection) or run one thing extra strong, like Norton 360 Deluxe (PCWorld’s high choose), it’s a must to guarantee its updates run every day to remain totally protected.
4. Use a password supervisor and robust passwords
Any password that you could simply keep in mind isn’t a robust password, and it’s best to by no means use the identical password on a couple of website. To guarantee all of your passwords are strong and to make it simpler to alter them every so often, use a password supervisor like Dashlane or Keeper.
This will prevent plenty of complications in case you ever want to alter all of your passwords after an assault, and likewise preserve your passwords encrypted in order that attackers gained’t be capable of learn them out of your laborious drive. (If you ever do get contaminated with ransomware, make your password supervisor the primary account credential you replace, because it has all of your different credentials in it.)
How to outlive a ransomware assault
1. Take a deep breath
Ransomware is so frequent as a result of it’s an efficient means for attackers to get cash out of victims. The risk preys on a mixture of weaknesses in each the PC’s safety and the consumer’s feelings. Attackers are relying on you to lose your cool and pay up promptly. But don’t let your feelings get the very best of you. Take a deep breath and end up a information (like this one!) to guide you thru subsequent steps.
2. Don’t interact the attackers
Ransomware assaults are automated, that means the people behind the assault aren’t straight acutely aware of you or your PC. At the second of the assault, you is likely to be little greater than a line-item in an exercise log they haven’t checked out but, so don’t elevate your profile by calling any numbers displayed on the display screen or in any other case interacting with the malware.
Don’t observe any hyperlinks, e mail any addresses given to you, or pay any ransoms. Engaging with the attackers will solely improve their concentrate on getting what they need from you, subjecting you to additional danger, and paying the ransom is not any assure that you simply’ll get your information again.
3. Disconnect your system from the web
As shortly as you may, take your system offline to stop it from sending your information to attackers or infecting different units in your community. If you’re on an ethernet connection, merely disconnect the wire instantly. If you’re on your house Wi-Fi community, strive disconnecting via your PC’s Wi-Fi settings or change to airplane mode in case you nonetheless have sufficient management of the PC to do this.
Whether that works or not, enter your router’s menu from one other system and determine your PC on the purchasers checklist, then block that machine from accessing the community by accessing the Access Control or Blacklist menu (this may increasingly have a distinct however related title on your house router).
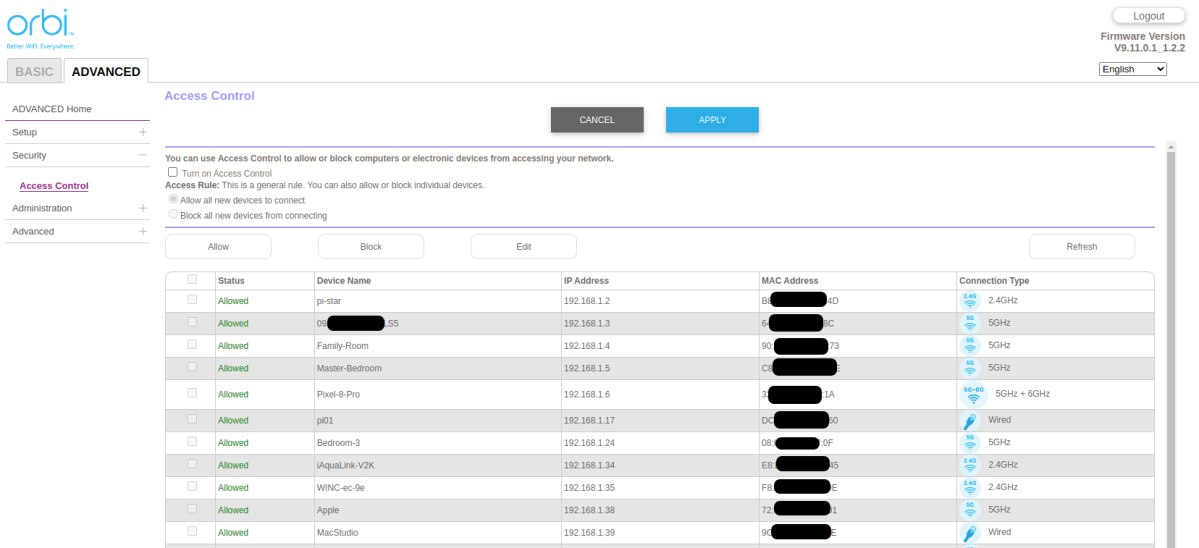
Use your router’s Access Control menu to dam your contaminated PC from rejoining your community till you’ve totally eradicated any ransomware.
Robert Strohmeyer/Foundry
4. If that is your work PC, notify your IT supervisor instantly
Consumers usually are not the perfect goal of ransomware assaults, as a result of they usually don’t find the money for to pay the actually massive ransoms and if their private pictures are backed up on one other system, they may not care sufficient to pay the ransom. But if for some motive, your work laptop has been attacked, contact the IT division. It has a vested curiosity in helping you posthaste.
5. Change all of your passwords
Some ransomware can seize and ship your information to its controllers in an effort to steal helpful monetary info, web site credentials, or different information that can be utilized to hold out additional assaults or identification theft. So, now’s the time to start out altering your passwords on all of your on-line accounts.
If you’re utilizing a great password supervisor like Dashlane or Lastpass, that may aid you automate the method a bit. If not, you’ll must do it by logging into every account and manually altering your passwords. Prioritize your e mail account first, so it could’t be hijacked and used to worsen the assault in your information and identification. Then go to your monetary accounts, your main cloud accounts akin to Google and Apple, your ISP and cell service, after which the whole lot else within the lengthy tail of internet sites you employ.
Don’t neglect to alter your Wi-Fi password, too, for good measure. Literally any credential you’ve ever used on that PC wants to alter as a result of all of it’s more likely to find yourself on the darkish internet shortly after the assault.
A password supervisor like Dashlane makes it simpler to guard your passwords in case your system is compromised, and might automate altering passwords on all of the websites you employ.
PCWorld / Dashlane
6. Preserve proof… or take away the PC’s drive… or try information restoration
Once you’ve remoted the PC out of your community and the web, there’s little the ransomware can do in addition to full its encryption course of in your laborious drive. Malware consultants usually agree that trying to cease the encryption by shutting down the PC is dangerous, as a result of it might render your complete drive unrecoverable. What you select to do subsequent relies on a number of elements.
Is it your private PC or a piece machine? Do you wish to get regulation enforcement concerned? Do you want to recuperate the information or can you reside with out it? Each of those questions will lead you down a distinct path.
If you’re utilizing a piece PC, it’s best to have already contacted your IT division by this level, and also you’ll observe their directions for all subsequent steps. They’ll virtually definitely advocate altering all of your passwords, simply as we’ve got right here, however may need you to do a number of extra steps associated to submitting incident stories and locking down entry to firm techniques. Some corporations may also require you to take some type of cybersecurity coaching earlier than providing you with again full entry to their techniques.
If your private PC has been attacked, it’s possible you’ll or might not wish to get regulation enforcement concerned. The FBI has a cybercrimes unit, and you’ll file a criticism with them at www.ic3.gov. If you do contain regulation enforcement, you’ll wish to protect as a lot proof as doable, which can embody turning over the affected laborious drive so investigators can decide what sort of malware was used and probably determine the attackers. Whether or not all this problem is price your whereas is a matter of debate, however it’s possible you’ll really feel higher understanding you’ve contributed to the reason for combatting one of these crime.
Whether or not you select to contain regulation enforcement, determine how essential it’s to you to get your information again. If you hand over your laborious drive as proof, it might be some time earlier than you see it once more, so any information restoration effort ought to be made previous to giving the drive to the authorities. While there are methods to probably decrypt the drive your self, the chance that you simply’ll find yourself infecting the pc you employ for the restoration course of, or simply wind up destroying the encrypted information within the course of, is larger than the likelihood of efficiently recovering the information with out making issues worse.
For this motive, I like to recommend contacting an information restoration service that makes a speciality of ransomware restoration, akin to OnTrack, for the very best shot at getting the information again safely. Just remember that specialty information restoration providers aren’t low cost and should not even work, and generally you’ll must pay for the service whether or not or not the restoration is profitable.
If you’d slightly save your cash and transfer on, and don’t even care about getting the information again, your finest wager is solely to take away and retailer the contaminated laborious drive in a closet in case you later go for restoration providers. The value of laborious drives is now so low that there’s little motive to prioritize salvaging a tough drive over establishing whole certainty that the malware doesn’t survive to reinfect your PC.
Now, in case you don’t intend to recuperate the information, merely destroy the bodily laborious drive by taking it all the way down to your native shredder service. If you may’t afford to switch the laborious drive, at the very least make sure to totally repartition it in order that the Master Boot Record and all present partitions are fully erased and there’s no place left for the malware to cover. With a recent drive put in, re-install Windows and restore no matter backups you could have available, then transfer on together with your life.

