Operating methods want at the very least a minimal of upkeep to run correctly over the long run. While some vital instruments are already included from Microsoft, many professionals need or want extra highly effective and helpful instruments to assist them when utilizing Windows methods.
Thankfully, Microsoft supplies quite a few instruments freed from cost that assist with evaluation, upkeep, and troubleshooting. Some of those instruments are helpful for everybody in on a regular basis use, whereas others are solely wanted in particular conditions.
There are a number of the explanation why the instruments will not be included as customary Windows gear. Due to the sheer variety of completely different features, the necessity for these particular instruments is commonly not apparent at first look, and generally the stipulations for utilizing the instruments must be created first. In this text we’ll clarify the best way to use Microsoft Sysinternal instruments as a way to carry out crucial upkeep or analyze and troubleshoot issues in Windows optimally and effectively.
In the previous, should you needed to develop system-related instruments for Windows, you wanted in-depth information of the working system. That was till 1996 when the programmers Mark Russinovich and Bryce Cogswell programmed diagnostic software program for Windows for his or her firm Winternals Software LP. In 2006, Microsoft took over the corporate and commenced distributing this software program themselves.
Under the title “Sysinternals,” these instruments are regularly developed and tailored for newer Windows variations resembling Windows 10 and 11 and made out there for obtain freed from cost. Some of the instruments provide a graphical consumer interface, whereas others are began through Powershell or the command immediate. Under “Download” you’ll discover the person instruments and likewise the Sysinternals suite, which accommodates nearly the entire 60-plus instruments.
Set up Sysinternals instruments conveniently: The Windows System Control Center (WSCC) downloads the instruments and supplies brief descriptions.
IDG
However, we advocate the Windows System Control Center (WSCC) for putting in the Sysinternals instruments. It downloads both all or solely the specified applications from Microsoft and likewise takes care of updating these instruments sooner or later.
Once you obtain WSCC, place it right into a folder with a brief title and no areas or particular characters, for instance “C:WSCC” or “C:ToolsWSCC”. This makes it simpler to make use of the command line instruments.
When you begin it for the primary time, you’re in a position to set some choices. However, it’s normally enough to easily verify with “OK“. In the “Software Sources” window, choose the device packages for set up. Click on “OK” after which on “Yes“. In the subsequent window, you possibly can specify the set up path. Accept the default “. SysInternals Suite” by clicking on “OK“. Then click on on “Install” to obtain all instruments or you possibly can take away the verify marks from these you don’t want.
WSCC exhibits the class “Sysinternals Suite” within the tree view on the left facet of the window and teams resembling “File and Disk“, “Network” and “Security” beneath it. The listing with the related instruments seems on the suitable facet of the window. Next to every program there’s a button to begin the device and generally a “?” button that results in the assistance file.
The Sysinternals suite accommodates some applications with a further “64” of their title. These are the 64-bit variations. In WSCC you possibly can set a verify mark in entrance of “Launch the 64-bit model if out there” through “Settings” beneath “General“. Then, if out there, the 64-bit device might be began.
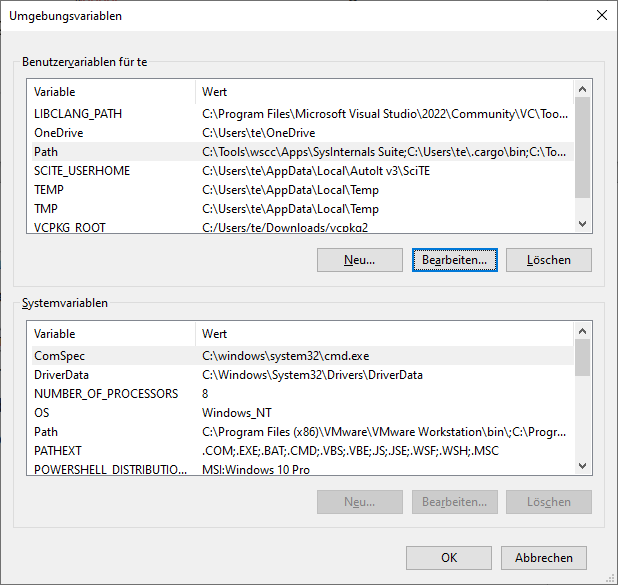
Configuration for the command line: So that the instruments may be began within the Powershell or command immediate with out specifying a path, configure the surroundings variable “Path“.
IDG
Configuration for the command line instruments
You can begin every device through the Windows Explorer or the command immediate immediately from the obtain listing. In Powershell or Command Prompt it’s crucial to place the listing in entrance of this system title. This may be averted by together with the folder within the surroundings variable “Path“. For the configuration, seek for surroundings variables within the “Settings” (Win-I) and click on on “Edit surroundings variables for this account” within the search outcome. Click on “Path” beneath “User variables” after which on “Edit“. Use “New” so as to add the listing wherein the Sysinternals instruments are situated. These can then be began just by their title.
Process Explorer: What is at the moment working on the PC?
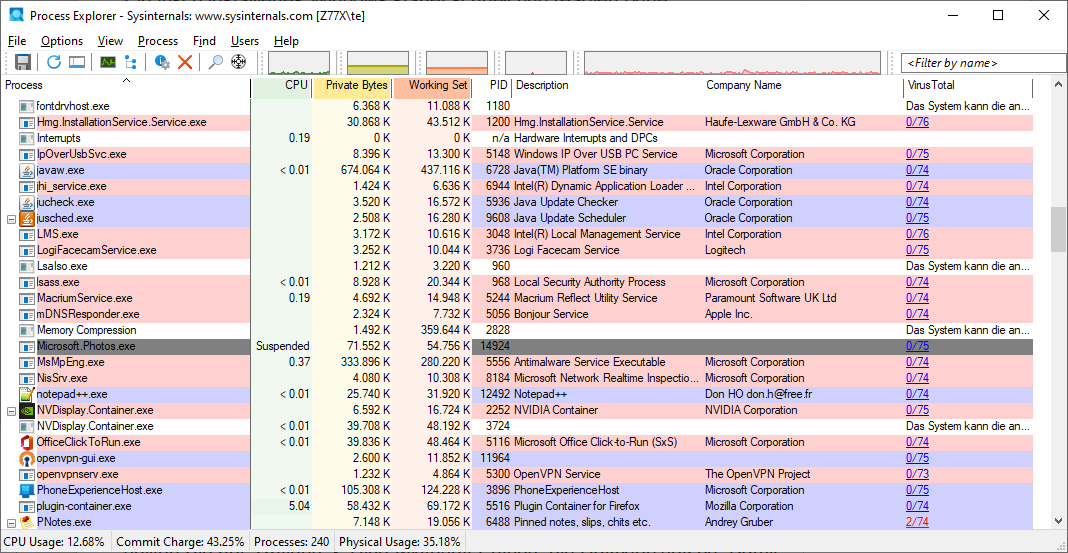
Process Explorer: The device exhibits all working processes with names and descriptions and supplies info on CPU load and reminiscence necessities.
IDG
While your laptop is working, purposes that you’ve got began your self in addition to quite a few background processes and providers are working in your laptop. The Windows Task Manager, which may be began with Ctrl-Shift-Esc, exhibits the entire purposes at the moment working in your laptop. When Task Manager is open beneath Windows 10/11, first click on on “More particulars” on the backside left after which go to the “Details” tab to see a listing of all working applications. Windows 11 customers from model 22H2 onwards can simply immediately click on on “Details” within the left-hand pane.
The Sysinternals device Process Explorer (Procexp.exe, Procexp64.exe) gives much more features than the Windows Task Manager. The program exhibits you what’s at the moment taking place on the PC by way of coloured backgrounds. Processes which have simply been began are highlighted in inexperienced, these which might be being terminated seem in purple.
By clicking on the column headers, this listing may be sorted by title, processor load (“CPU”), and reminiscence load (“Private Bytes”). This permits you to discover purposes that occupy a variety of primary reminiscence or place heavy calls for on the processor.
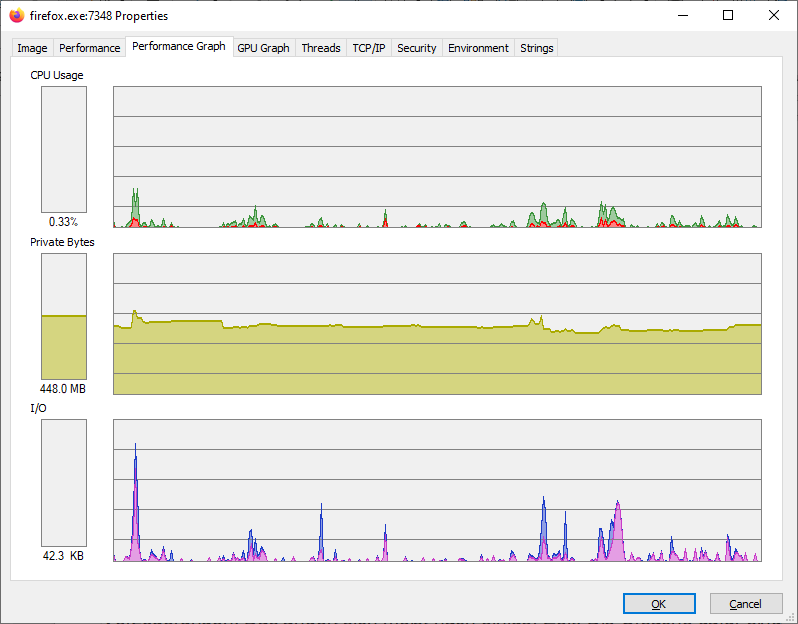
Clicking on “Properties” within the context menu supplies extra detailed insights. The tabs “Performance Graph” and “GPU Graph” give you a graphical overview of the processor and reminiscence actions over an extended time period. And the “TCP/IP” tab exhibits you which of them community assets an software is at the moment accessing.
If a course of crashes, it may be terminated through “Kill Process” beneath the context menu merchandise or restarted through “Restart“. Be conscious nonetheless that this solely works when you’ve got the mandatory entry rights. If not, go to “File -> Run as Administrator” to begin Process Explorer with the mandatory rights.
Dangerous processes?
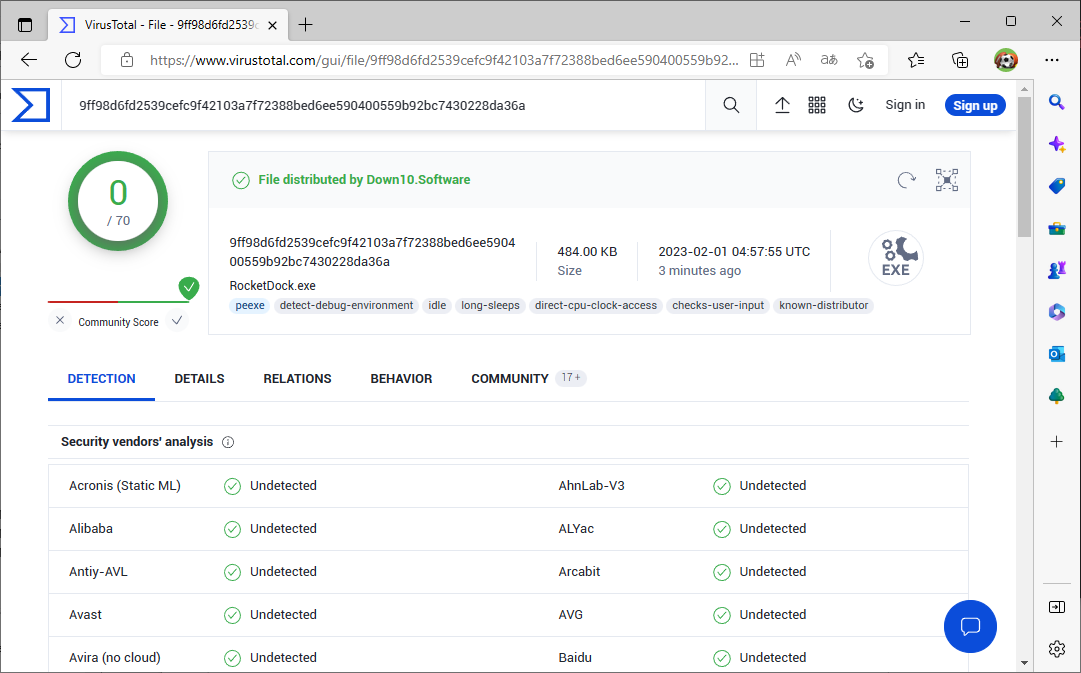
If sure processes appear suspicious, go to “Search Online” within the context menu. This will begin an Internet seek for the method title within the browser, which is able to give you additional info. If you believe you studied that it’s malware, go to “Check Virustotal.com” within the context menu. The first time you name it up, you’ll want to substantiate the phrases of use of www.virustotal.com. To take a look at all working applications, go to “Options -> VirusTotal.com -> Check VirusTotal.com“.
In the column “VirusTotal” you’ll be capable of see the outcomes of the virus scan. If a program exhibits “0/75”, for instance, you possibly can in all probability really feel secure classifying classify the file as innocent. If “1/75” seems, one among 75 virus scanners has discovered a suspicious file. Click on the Virustotal outcome to open the take a look at report within the browser. If just one or two virus scanners have reported anomalies, you possibly can assume that they’ve detected a virus by mistake — a false alarm. If there are extra, it may be malware. In this case, click on on “Behavior” or “Community” on the Virustotal web site to search out out extra in regards to the file. If unsure, uninstall the affected program and completely scan the system with up-to-date antivirus software program.
Autoruns: Reduce computerized program begins
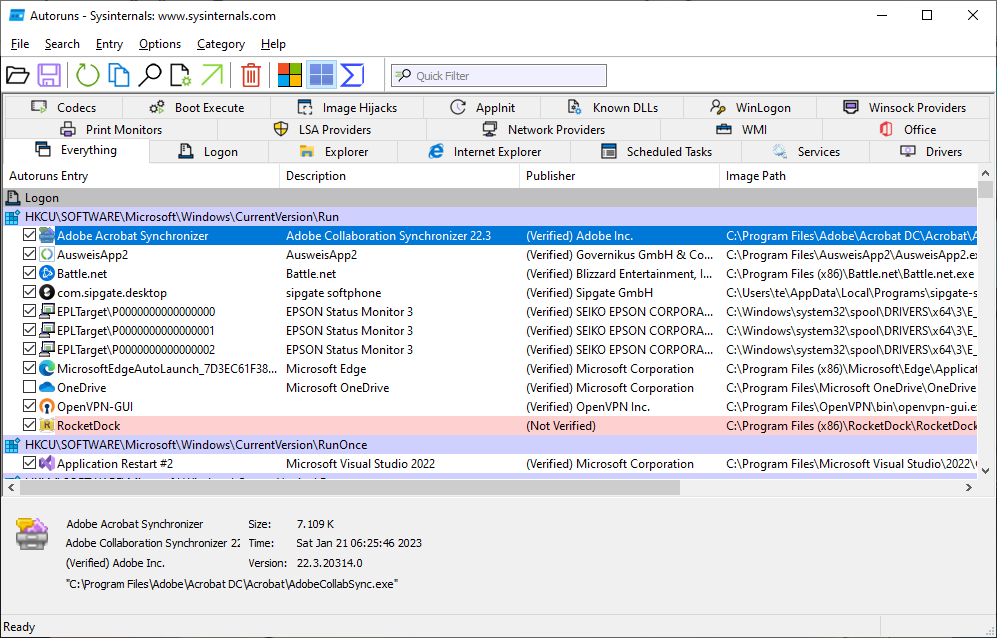
Automatic begins beneath management: Autoruns exhibits all autostart ramps. For applications you do not want, merely take away the tick in entrance of their title.
IDG
As most individuals know, a freshly put in Windows boots shortly and reacts with out delays. Unfortunately, this normally adjustments over time. The purpose for this slowdown is because of applications that configure themselves for computerized begin throughout set up. A program like this will then, for instance, verify for updates or anticipate occasions within the background. However, this delays the Windows begin and slows down the system. None of the auto-start applications are actually crucial, however they are often helpful. You should due to this fact weigh up in every case whether or not an auto-start program is vital to you and whether or not you need to settle for a delayed system begin for it.
Sysinternals-Autoruns
Sysinternals-Autoruns (Autoruns.exe, Autoruns64.exe) lists all auto-start ramps and may show and handle extensions for Windows Explorer and Microsoft Office.
After beginning, the device exhibits a number of tabs for the completely different areas. You’ll discover that probably the most sensible tab is the “Everything” tab which shows all the things collectively. The listing is kind of lengthy, however may be restricted through “Options -> Hide Microsoft Entries” to cover merchandise that don’t originate from Microsoft and solely present software program that was added later from different producers.
Remove the ticks from all entries that you do not want—this doesn’t delete something. If it seems later {that a} program must be began routinely in spite of everything, you possibly can all the time verify the field once more.
Use “File -> Run as Administrator” to begin Autoruns with elevated rights. As a rule, this isn’t crucial until, for instance, system providers are to be switched off beneath “Services“. However, warning is suggested right here. Do not swap off Microsoft providers, as a result of this will result in malfunctions.
Save and evaluate
After you put in some software program in your laptop, new auto-start entries will in all probability seem. To keep away from having to seek for them, save the present state in a file through “File -> Save“. Later, the saved state may be in contrast with the present configuration through “File -> Compare“. The device highlights new entries in inexperienced, deleted entries seem in purple.
Examine processes extra intently
Sometimes it isn’t clear which program is hidden behind an auto-start entry and what its perform is. As with Process Explorer, by right-clicking in your mouse, you possibly can choose “Search Online” and thus begin an Internet search within the browser for the method title.
Check safety: Send suspicious information to Virustotal.com. The outcome exhibits whether or not a number of virus scanners discover malware within the file.
IDG
You may perform a safety verify, much like Process Explorer, through the context menu merchandise “Submit File to VirusTotal” or “Check VirusTotal.com“. If Virustotal reviews a variety of virus detections, that subsequent program must be examined extra intently and, if unsure, deleted or renamed.
Process Monitor: Examine the habits of applications
A virus scanner can detect malware in a program or classify it as harmful due to its habits. However, you may as well study which particular person information, registry entries, or community assets a program accesses by yourself and thus uncover any undesirable habits.
This kind of knowledge may be decided with the assistance of the Process Monitor (Procmon.exe, Procmon64.exe). However, this isn’t a straightforward activity, as a result of nearly all applications always entry the exhausting disk or the community, and it’s troublesome to filter out the related info from the lots of knowledge.
Process Monitor: The device exhibits which system assets a program is accessing. For instance, registry, file and community accesses may be decided.
IDG
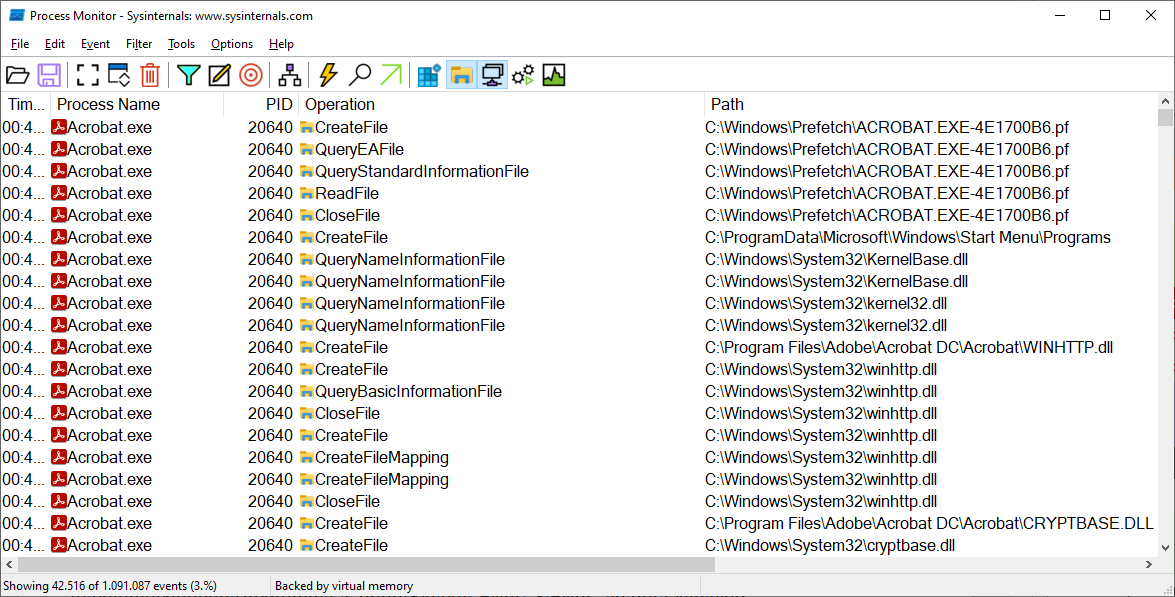
Monitoring begins instantly after the Process Monitor is began. You can cease the recording after a short while with the important thing mixture Ctrl-E. The program window exhibits a chronological listing of accesses from all lively applications. Under “Process Name” you’ll discover the title of this system that carried out an motion, beneath “Operation” the motion. For instance, “RegQueryValue” implies that this system has queried a worth from the registry.
A filter can be utilized to look at a selected software program. Open this system you need to study, click on on the icon with the goal (“Include Process from Window”) within the Process Monitor, maintain down the left mouse button and drag the crosshairs to the window of this system you need to study. Go to “Filter -> Filter“. There ought to already be some entries within the listing and you may, for instance, exclude Procmon.exe itself from the examination. At the start is the road “PID is [ID] embody”, the place “[ID]” is the method ID of the chosen program. In the principle window of Process Monitor, activate the recording with the important thing mixture Ctrl-E.
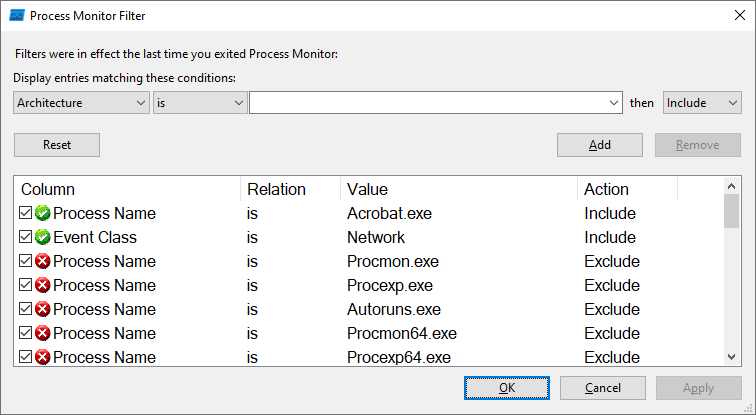
Create a filter for Process Monitor: Use a filter to limit logging to occasions which might be vital to you, resembling community entry.
IDG
For another configuration, go to “Filter -> Filter” and click on on “Reset“. Under “Display entries matching these situations” choose the entry “Process Name“. To the suitable, enter “is” and after it the title of this system you need to study, together with the file title extension “.exe“. At the tip of the road, choose “Include“. Then you’ll need to decide this system title, for instance, through Process Explorer. If crucial, outline additional filters resembling “Event Class is Network embody” should you’re solely focused on community entry, or “Event Class is File System embody“. Click on “Add” and eventually on “OK“.
After you’ve set your filter choice, delete the occasions recorded you’ve to date with Ctrl-X and begin the recording once more with Ctrl-E. The space displayed within the occasion listing will also be managed through the 5 buttons within the right-hand space of the toolbar.
Tip: The Sysinternals device Sysmon can be utilized to log all or chosen system occasions which will point out malicious code or hacker actions.
PS instruments: Command line instruments that will also be used for distant upkeep
Help for PS-Tools: The assist file Pstools.chm accommodates descriptions of the instruments and explanations for the that means of the out there command line choices.
IDG
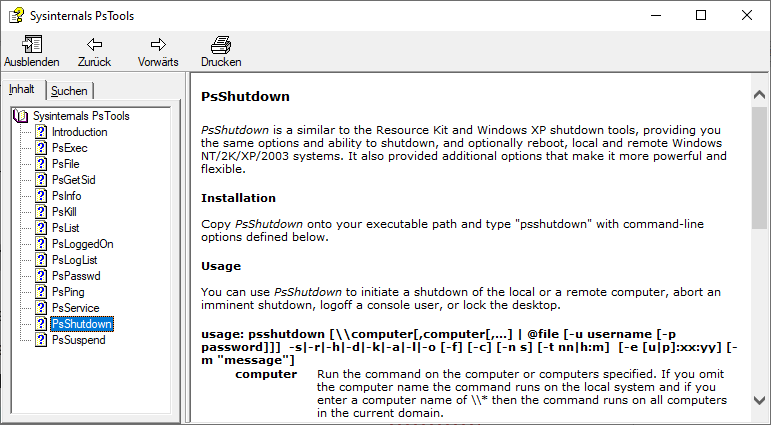
The Sysinternals instruments comprise a number of command line instruments whose names start with “PS”. With the PS instruments you possibly can show working processes, terminate processes, or shut down the PC. Help on the instruments is offered within the file Pstools.chm.
The instruments are notably fascinating as a result of they can be utilized to remotely management different PCs within the community. On the goal PCs, you will need to execute the next three command strains in a command immediate as administrator after which restart the PC:
sc config RemoteRegistry begin=auto
sc begin RemoteRegistry
reg add HKLMSOFTWAREMicrosoftWindowsCurrentVersionPoliciesSystem /v LocalAccountTokenFilterCoverage /t REG_DWORD /d 1 /fAlso just be sure you can entry community shares through Windows Explorer and that file and printer sharing is activated.
All instruments work on the native PC if you don’t specify some other choices. For distant entry, the instruments would require the IP tackle or title of the PC you need to entry. The normal type of the decision is
device.exe [IP] -u [Benutzer] -p [Passwort] [weitere Optionen]For duties that don’t require administrative rights, set the title of a regular consumer to “[user]”, in any other case use an account that has administrative rights. For instance
psexec [IP] -u [Benutzer] -p [Passwort] powershell.exeYou can use a Powershell interactively on the opposite PC. The command for that’s:
psshutdown -r -t 10 [IP] -u [Benutzer] -p [Passwort]The distant PC will restart after 10 seconds.
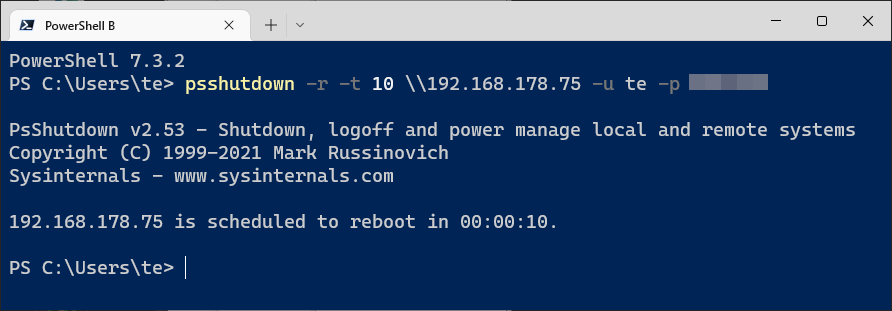
Remote shutdown: With the device Psshutdown, a PC may be restarted through the community. The goal PC should be configured for distant entry.
IDG
Handle: Unblock blocked folders
Sometimes folders or information can’t be deleted or renamed. The error message then reads “The motion can’t be accomplished as a result of the folder (or a file in it) is open in one other program“. An identical message is acquired if you’re attempting to eject a USB drive however an open file is stopping it. Unfortunately, Windows doesn’t normally point out wherein program precisely the file or folder is open. The Sysinternals device Handle Viewer (deal with.exe, deal with64.exe) is a little more talkative. Run it in a Powershell or command immediate that you simply begin with administrative rights. You can name the device with:
deal with C:[MeinOrdner]Handle Viewer will show the entire path to the affected folder or file for the placeholder. It additionally outputs the title of this system, its course of ID, and the deal with ID. If this system remains to be working, you possibly can then shut it to cease the error message.
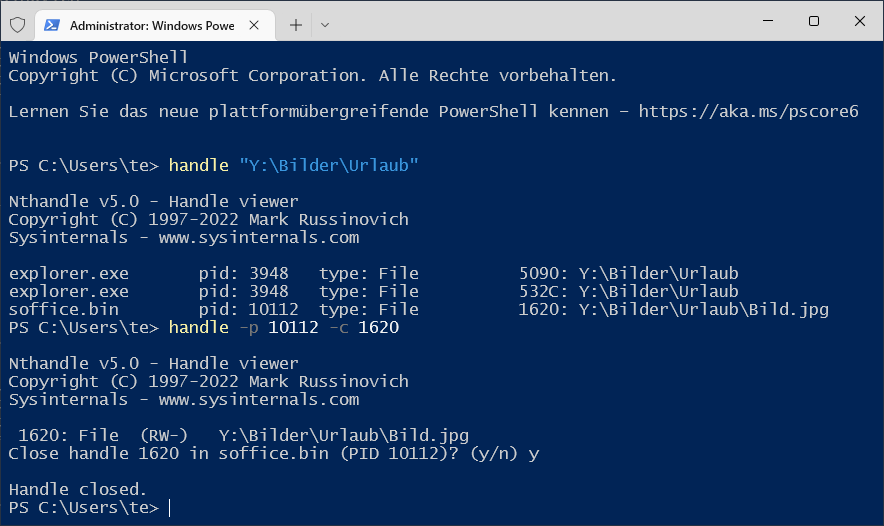
Who is obstructing a file? Handle exhibits which course of has simply opened a file completely. If crucial, the file deal with will also be closed.
IDG
If the programme has crashed within the background, shut the deal with by getting into the command:
deal with -p [Prozess-ID] -c [Handle-ID]Once you do, solely the deal with might be closed, this system itself normally continues to run. For unsaved information, nonetheless, this can in all probability end in knowledge loss so watch out.
This article was translated from German to English, and initially appeared on pcwelt.de.

